Overview
The Microsoft Teams integration uses an application registration in Microsoft Entra ID and authenticates with Tenant ID, Client ID, and Client Secret. Microsoft documents this as the standard application-based method for accessing Microsoft Defender APIs without a user session.Supported Versions
| Component | Supported Version |
|---|---|
| Microsoft Defender XDR | Current cloud tenant |
| Microsoft Defender for Endpoint APIs | Current supported API set |
| Microsoft Entra ID | Current supported cloud directory |
| AirMDR Platform | Current supported cloud deployments |
Microsoft provides separate but similar app-registration guidance for Microsoft Defender XDR and Microsoft Defender for Endpoint, both using Microsoft Entra application authentication.
Authentication
AirMDR uses application-based OAuth authentication through Microsoft Entra ID.| Credential | Description |
|---|---|
| Tenant ID | Directory (tenant) identifier from the Microsoft Entra app |
| Client ID | Application (client) identifier from the Microsoft Entra app |
| Client Secret | Secret generated under the app registration |
| Remote Agent | Optional AirMDR routing component selected in AirMDR, not generated in Microsoft Defender |
Pre-requisites
Set Up Steps
Register a Microsoft Entra Application
- Log in to your Azure Portal.
- Go to Microsoft Entra ID (formerly Azure AD).
- In the left menu, click Manage → App registrations.
Register a New Application
- Click + New registration.
- Provide the mandatory details:
- (Application Name: Enter a name for your app (e.g.,
airmdr-defender). - Supported Account Types: Select “Accounts in any organizational directory (Any Microsoft Entra ID tenant - Multitenant)” option).
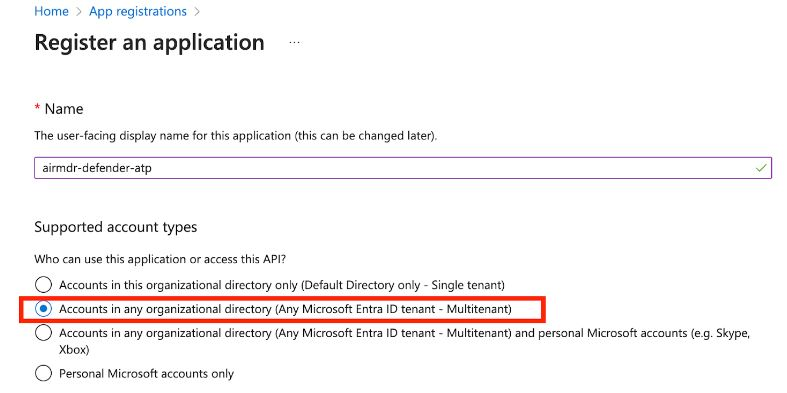
- (Application Name: Enter a name for your app (e.g.,
- Click Register.
Retrieve the Application (Client) ID and Tenant ID
- After successful registration, you will see the App Overview page.
Copy Application (Client) ID – Identifies your app.
Copy Directory (Tenant) ID – Identifies your Azure AD tenant.
Configure API Permissions
- In the application Overview page left navigation pane, select Manage dropdown.
- Click API Permissions.
- Click + Add a permission
- Select APIs my organization uses tab.
- Search and select the API “Microsoft Threat Protection”.
- Click on Application permissions.
- Select the required permissions:
- To Fetch List of Incidents -
Incident.Read.All
- To Fetch List of Incidents -
- Click Add permissions at the bottom of the page.
- Click API permissions, select Yes for Grant admin consent confirmation to allow access.
Create a Client Secret (For Authentication)
- In the application Overview page left navigation pane, select Manage dropdown.
- Click Certificates & secrets.
- Click + New client secret.
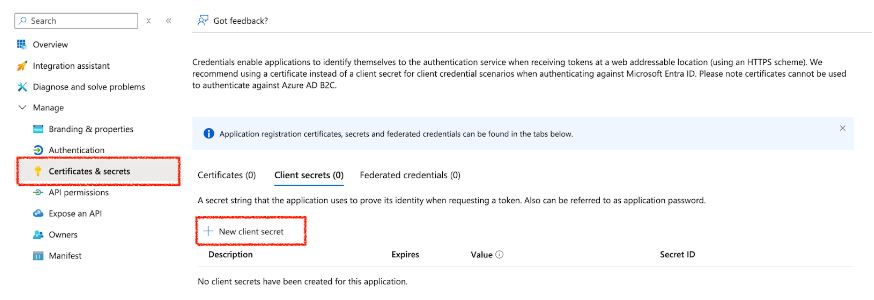
- Enter a description (e.g.,
MySecretKey) and set expiration. - Click Add.
Email the Tenant ID, Client ID and the Client Secret Value to AirMDR or self Configure Microsoft Defender in AirMDR Integrations Dashboard.
Evaluate Microsoft Defender
Pre-requisites
Azure App Registration with API permissions for Microsoft Defender.
Client ID, Tenant ID, and Client Secret.
Obtain an Access Token
Open cURL and run the following command to check if your API Access is working:MDE uses OAuth 2.0 authentication. First, request an access token from Microsoft Entra ID (Azure AD):Replace:
<tenant_id>– Your Azure Directory (Tenant) ID.<client_id>– Your App Registration Client ID.<client_secret>– Your App Registration Client Secret.
- This verifies if the user can retrieve device information based on the assigned scope.
Configure Microsoft Teams in AirMDR Integrations Dashboard
- Navigate to AirMDR, provide the credentials and click Login
- Navigate to the AirMDR Integrations Dashboard in the left navigation pane and select Integrations.
- Use the search option, enter the keyword “Microsoft Defender”, select the Connections tab, and click + Create button.
- Enter an unique name to the Instance (e.g.,
your org name-Microsoft Defender) to easily identify the user connection by AirMDR. - Enter the generated Tenant ID, Client ID and the Client Secret in the Authentication Details field params, and click Save.
Skills provided by this Integration
| Skill ID | Purpose |
|---|---|
| List Microsoft Defender Incidents for Detections | Fetches and normalizes all security incidents from Microsoft Defender XDR using the Incidents API (GET /api/incidents on api.security.microsoft.com) with full pagination support for detection workflows. Microsoft Defender XDR aggregates incidents across all Defender services — Endpoint, Identity, Cloud Apps, Office 365, and Sentinel. Each incident is expanded into alert-level rows using Spark SQL, producing a normalized dataset with incident metadata (ID, name, severity, status, classification, determination, assigned analyst) and per-alert fields (alert ID, title, category, severity, status, service source, detection source). The duration and duration_type parameters scope results to a rolling time window via OData filter on createdTime or lastUpdateTime. Use this skill as the detection entry point for automated triage, alert correlation, and scheduled detection pipelines. |
| List Microsoft Defender Incidents | Retrieves a paginated list of security incidents from Microsoft Defender XDR using the Incidents API (GET /api/incidents on api.security.microsoft.com). Microsoft Defender XDR aggregates incidents across all Defender services - Endpoint, Identity, Cloud Apps, Office 365, and Sentinel - into a unified incident queue. Each incident object includes the incident ID, name, severity (Informational, Low, Medium, High), status (Active, Resolved, Redirected), classification, determination, assigned analyst, creation and last update timestamps, and a nested list of alerts from the originating Defender services. The duration and duration_type parameters construct an OData filter applied against either createdTime or lastUpdateTime, scoping results to a rolling time window. Use this skill for SOC triage, daily alert review, or SIEM enrichment. Pivot to get_microsoft_defender_incident for full incident details including alerts, devices, and entities. |
| Get Microsoft Defender Incident | Retrieves full details of a single incident by ID from Microsoft Defender XDR using the Incidents API (GET /api/incidents/ on api.security.microsoft.com ). The response includes the complete incident object with incident ID, name, severity (Informational, Low, Medium, High), status (Active, Resolved, Redirected), classification, determination, assigned analyst, creation and last update timestamps, and the full list of associated alerts. Each alert contains the alert ID, service source (indicating the originating Defender service such as MicrosoftDefenderForEndpoint, MicrosoftDefenderForldentity, MicrosoftCloudAppSecurity, MicrosoftDefenderForOffice365), title, description, severity, status, category, devices, and entities. Use this skill during incident triage to get the full attack chain across all Defender services, or during incident response to understand the scope and impact of a specific incident. Obtain incident IDs from list_microsoft_defender_incidents. |
Additional Information
🧰 Troubleshooting Authentication Issues
🧰 Troubleshooting Authentication Issues
| Error Code | Possible Issue | Solution |
|---|---|---|
| 401 Unauthorized | Invalid token | Regenerate token, check credentials |
| 403 Forbidden | Insufficient API permissions | Grant admin consent in Azure Portal |
| 400 Bad Request | Incorrect request format | Verify API endpoint and headers |
| 500 Internal Server Error | Service issue | Retry later, check the Defender status |
🛑 Security & Access Best Practices
🛑 Security & Access Best Practices
- Secure service account credentials
- Use built-in RBAC from Microsoft Defender for Endpoint and related Defender services.
- Assign only the minimum required permissions using Microsoft Entra ID roles.
- Enforce:
- Multi-Factor Authentication (MFA)
- Device compliance checks
- Location-based access restrictions
- Ensure all endpoints:
- Are onboarded to Microsoft Defender for Endpoint
- Meet compliance policies
- Enable:
- Attack Surface Reduction (ASR) rules
- Endpoint Detection and Response (EDR)
- Disable:
- Unnecessary services and ports
- Ensure encryption:
- In transit → TLS 1.2+
- At rest → Microsoft-managed or customer-managed keys
👉 Support & Maintenance
👉 Support & Maintenance
- 📧 Contact AirMDR Support through your designated support channel.
- 🔁 Rotate:
- Client secrets (recommended every 30–90 days)
- Certificates before expiration
- Implement automated rotation where possible
- 🔄 Reconnect in AirMDR when secrets are changed.

